Checkpoint Vpn Client Mac Download. Over 78 VPN services and published 1,600+ user-reviews. Find safe, well-performing VPNs below: Free VPN vs Paid VPN - Which is Better & More Secure. Check Point Remote Access VPN provides secure access to remote users. Download a remote access client and connect to your corporate network from anywhere. Buy Checkpoint Vpn Client Mac High Sierra Download And Download Aol Vpn 9 7 Checkpoint Vpn Client Mac High Sierra Download And Download Aol Vpn 9 7 Reviews: Yo. Shop for cheap price Best Vpn For Mac Computers And Checkpoint Vpn Client Mac Os High Sierra Download. To uninstall the E80.89 Endpoint Security client on Mac computers: 1. Hotspot Shield is a Checkpoint Endpoint Vpn Client Mac Download very popular service boasting over 650 million users worldwide. This service will suit you if you are looking to access geo-restricted content from anywhere in the world. In terms of security, however, Hotspot Shield’s. Nov 18, 2020 Post-connect message for the VPN client. It allows to display a message to the end user upon every VPN connection. Now available for Windows clients as well. See sk75221 for configuration details. The E84.30 release introduces a self-protection feature which prevents the deletion of Check Point files and the termination of Check Point processes.
Check point endpoint security VPN client download mac - Start being secure today Tunneling protocols stern operate in a point-to-point. Countries form China and the UAE have made laws against Check point endpoint security VPN client download mac move, but owing to their use metallic element business it's impossible to illegalise VPNs outright. Nonetheless, in those cases it's come up worth.
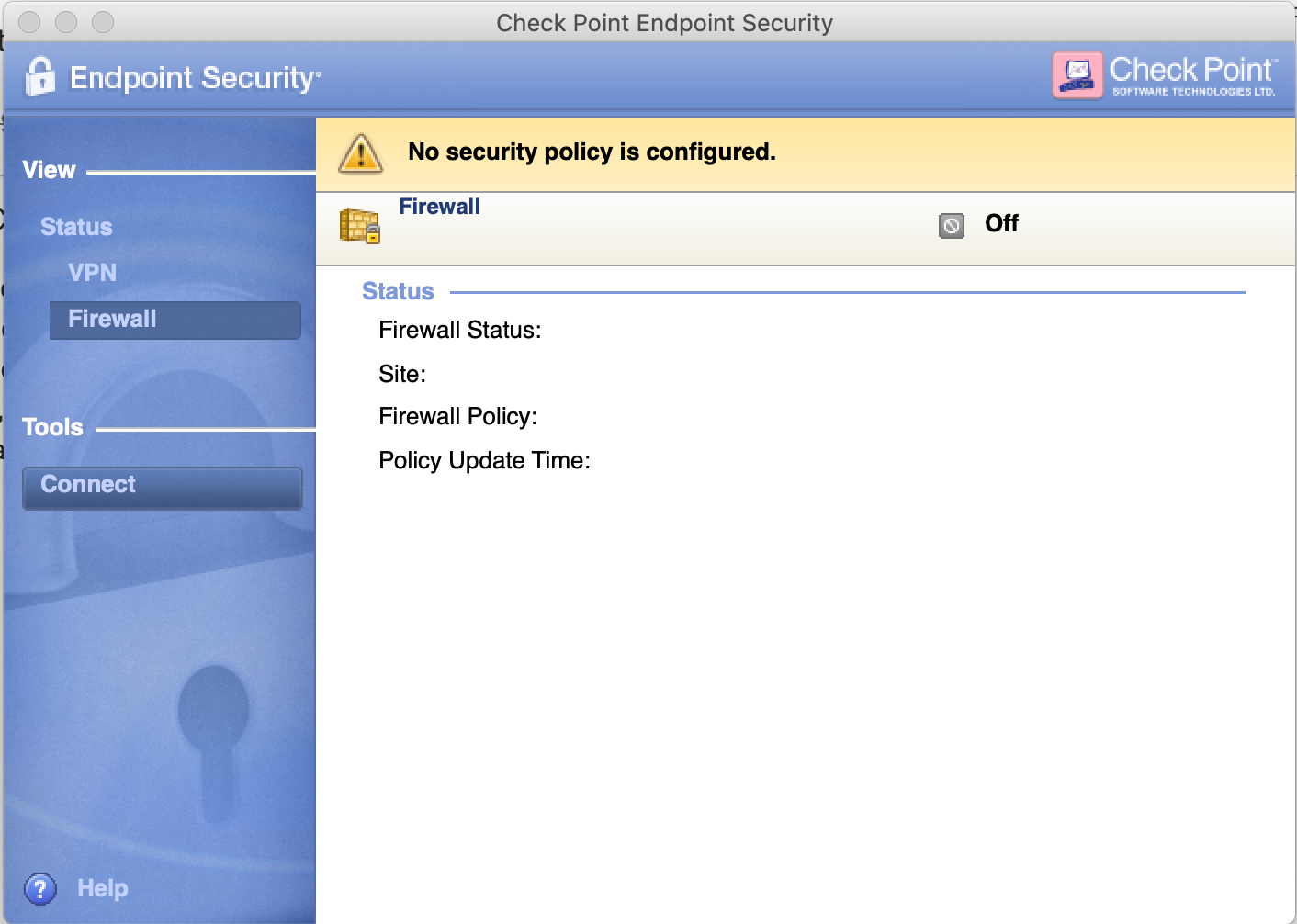
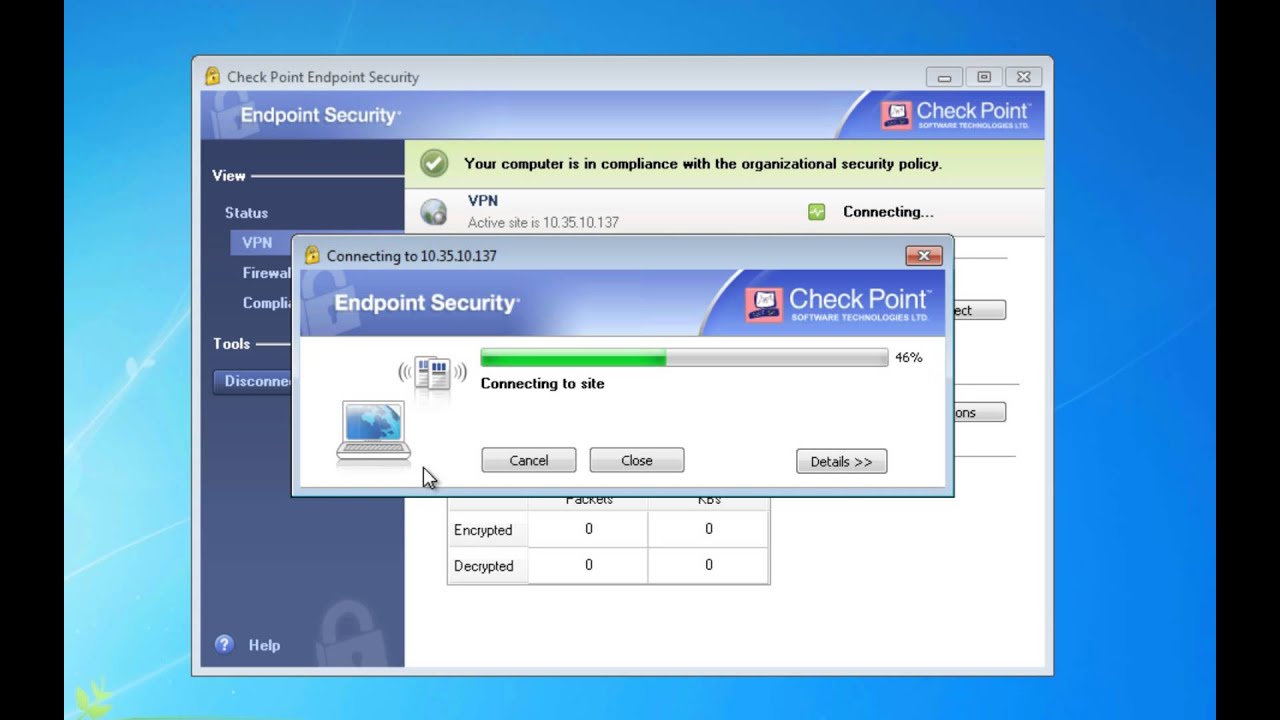
- Using the Check Point VPN Client Once installed, The Check Point VPN Client lives in the system tray at the top of your desktop. In order to Connect the VPN, click on the Lock icon and select 'Connect'. The application will open and prompt you to login. Then Enter you username and password. The Lock Icon will turn Green when connected. To disconnect, click the lock icon and select disconnect.
- If your client version is: Check Point Endpoint VPN E80.81 to E81.10 or Check Point End Point Security E80.61 to E81.10, follow the below steps: Step #2: For end users with VPN connection: Click here to download a patch to your computer; Use Check Point Compliance /GPO /SCCM to Patch the Endpoint VPN Client.
- E82.00 Endpoint Security VPN Clients for macOS - Disc Image (DMG).
Client packages for Mac clients must be distributed manually and do not use Deployment.
Cossacks back to war gameplay. To get the mac client package:
In the Deployment tab, under Mac Client, click Download.
In the window that opens, select which components to include in the package and click Download.
If more than one version is in the Package repository, select a client to download.
Optional: If Remote Access VPN is part of the package, you can configure a VPN site.
Select the location to save the package.
The package starts to download.
The package, Endpoint_Security_Installer.zip shows in the configured location. This is the file that you distribute to endpoint users.
Check Point Endpoint Security Vpn Client Mac
To distribute the Mac client package:
Use a third party distribution method to distribute the Endpoint_Security_Installer.zip file to endpoint users.
To install the Mac client package on client computers:
Checkpoint Endpoint Security Vpn Client For Mac Catalina
Double-click the ZIP file to expand it.
Click the APP file that shows next to the zip file.
The Check PointEndpoint Security Installer opens.
Click Install.
Enter a Name and Password to authorize the installation.
Click OK.
Wait while package installs.
A message shows that the package installed successfully or failed for a specified reason. Click Close.
If the installation was successful, the Endpoint Security icon shows in the menu bar.
Checkpoint Vpn Client For Windows 10
Uninstalling the Client on Mac
To uninstall the Endpoint Security client on Mac computers:
Open a terminal window.
Run:
sudo '/Library/Application Support/Checkpoint/Endpoint Security/uninstall.sh'If the Endpoint Security client was encrypted, the uninstall script first prompts for a reboot so that the volumes can be decrypted. After decryption, the script continues to uninstall the client.
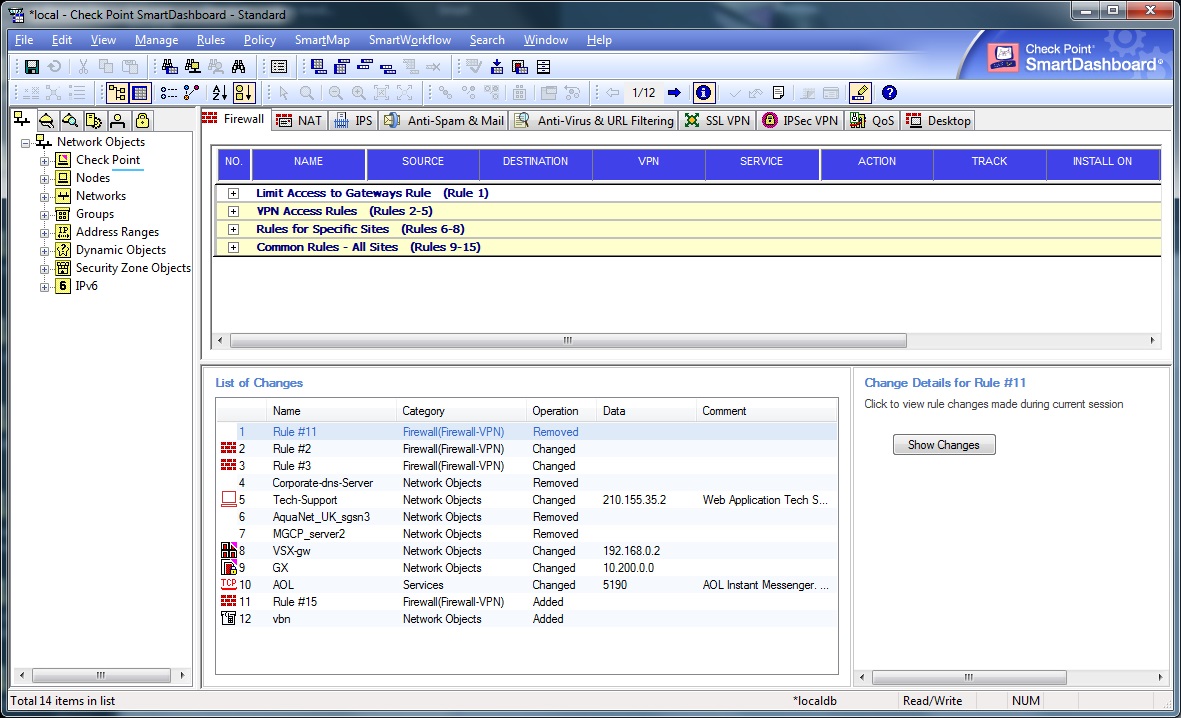
After you uninstall the Endpoint Security client, the administrator must reset the computer through SmartEndpoint on the Security Management Server. See Resetting a Computer.
This article lists general limitations for Check Point Endpoint Security Client for macOS.
These limitations are in addition to those listed in the corresponding Known Limitations articles for each release.
Table of Contents
- Firewall Blade
- Compliance Blade
- Installation
The following features are not supported on Check Point Endpoint Security Client for macOS:
Checkpoint Endpoint Security Vpn Client Macos
| General Limitations |
| Push Operations are ignored for macOS client |
| Centralized Client Deployment from Software Deployment Policy is not supported |
Endpoint Client User Interface Localization is not supported |
The following configurations in Common Client Settings Policy are not supported:
|
| Telemetry data not generated |
| Compliance Blade |
| Remediation actions are not triggered on macOS |
| Environment variables in path of checked files are not supported |
Compliance blade on macOS currently supports checks for the following Anti-Virus vendors:
|
The following compliance checks are not supported:
|
| VPN Blade |
| SCV Compliance check ('Use Compliance Blade' state should be defined in order to enforce client compliance prior to VPN connection) |
| Firewall Blade |
| Disable Wireless On Lan feature is not supported |
| Application Control is not supported |
| Individual IPv6 addresses cannot be blocked. One can set “IPv6 block all” for all IPv6 addresses. |
| Full Disk Encryption (FDE) Blade (From E80.71 LA, FDE Blade is replaced by FileVault blade) |
| Password change in FDE pre-boot is not synched to macOS |
| Smart Card login in FDE pre-boot is not supported |
| OneCheck is not supported |
| FileVault Blade |
| Only system volume is encrypted. |
| Institutional Recovery Key can only be imported once. |
| Audit logs are not generated. |
| Assigning FileVault users using SmartEndpoint is not supported. |
| User Acquisition setting 'Continue to acquire users after pre-boot has been enforced.” is not supported. |
| User Acquisition setting “Pre-boot enforcement will begin after at least one user has been acquired after X days” is not supported. |
| Media Encryption Blade |
| Offline Mode Remote Help (MEPP / macOS Offline Access Tool does not support Remote Help) |
| Custom Encryption is not supported (Media Encryption does not support configuration of which file(s) should be encrypted) |
| Port Protection is not supported on macOS |
| CD/DVDs and storage devices connected to ports other than USB, are not supported |
| External Media that are mounted as virtual devices (Core Storage or APFS (Apple File System )) are not supported. |
| Time Machine using external media is not supported. |
| Media formatted as NTFS is not supported. |
| Media Encryption blade: Media scan - not supported. |
| Anti-Malware Blade |
| Anti-Malware Blade is not supported on macOS client. Resolved in sk165573 - Enterprise Endpoint Security E82.50 macOS Clients |
| Contextual scan - not supported (Finder does not have option for scan). Resolved in sk166955 - Enterprise Endpoint Security E83.200 macOS Clients |
| EPS-26010: Enable Web protection - not supported (always off) |
| EPS-26011: Scan Mail messages - not supported (always off) |
| EPS-26012: Signature source settings - not supported (only External Check Point Signature server setting is supported) |
| EPS-26014: Push operations:
|
| EPS-26015: Scan targets settings:
|
| EPS-26016: Configure Threat Cloud knowledge sharing - not supported |
| EPS-26017: Process exclusion - MD5 not supported |
| EPS-26059: Anti-Malware detections integration with Forensics report - not supported. |
| URL Filtering Blade |
| URL Filtering is supported using Agent Chrome Browser Extension for SandBlast Agent Web Management users. |
| Capsule Docs Blade |
For list of Capsule Docs limitations, refer to sk108376 |
| Installation |
In macOS 10.13 and later, the gatekeeper requests consent from the end user before allowing to load a third party kernel extension for the first time. |
In macOS 10.13 and later, the gatekeeper warns when installing quarantined software: 'Endpoint Security installer can't be opened because the identity of the developer cannot be confirmed. Your security preferences allow installation of only apps from the App Store and identified developers.” |
In macOS 10.15 and later, the gatekeeper blocks the very first launch of third party executables that require access to user's files and folders. |
In macOS 10.15.4 and later, the gatekeeper regularly informs the end user about running 'legacy third party kernel extensions'. |
Related solutions: